Network Management Methods
Not sure you’re ready?
Take the ~3-minute readiness diagnostic and see where you stand.
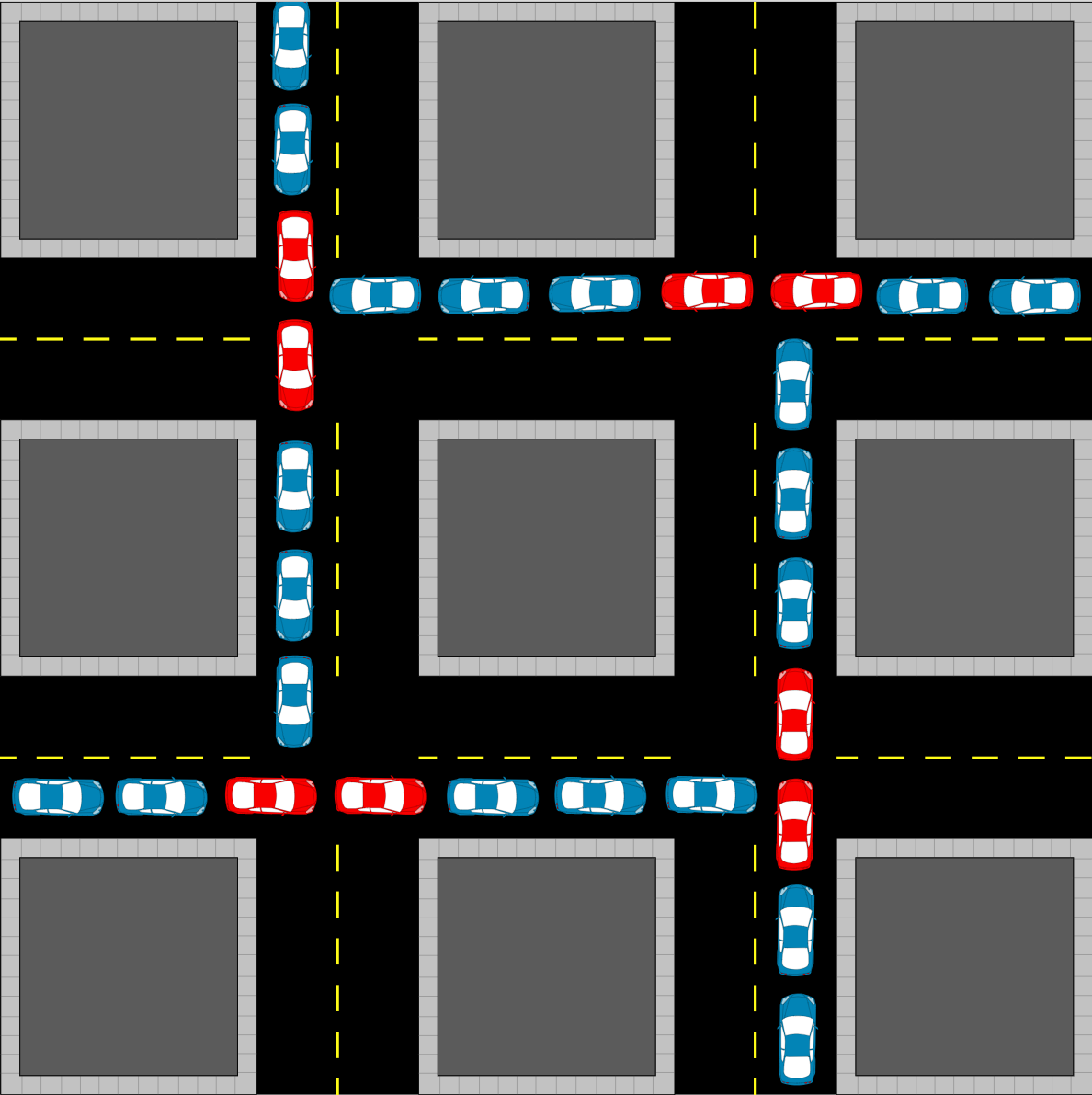
Imagine maintaining a vast, automated transit system where millions of vehicles speed through intricate intersections every second. You, the infrastructure engineer, cannot simply walk into the active traffic lanes to reprogram the signaling lights. You require dedicated access tunnels, encrypted communication frequencies, and heavily guarded control rooms to manage the system securely without disrupting the flow of traffic or exposing the controls to malicious actors. In enterprise networking, the routers, switches, and firewalls that direct immense volumes of data require similar specialized management pathways. Mastering how to securely access, configure, and rescue these devices is what separates the operators who keep the digital world moving from those who accidentally cause gridlock.
To manage a network effectively, we must understand the precise mechanisms of how we speak to our infrastructure. Network management is not merely about knowing which commands to type; it is fundamentally about how we safely deliver those commands to the device.