Time Protocols and Network Access
Not sure you’re ready?
Take the ~3-minute readiness diagnostic and see where you stand.
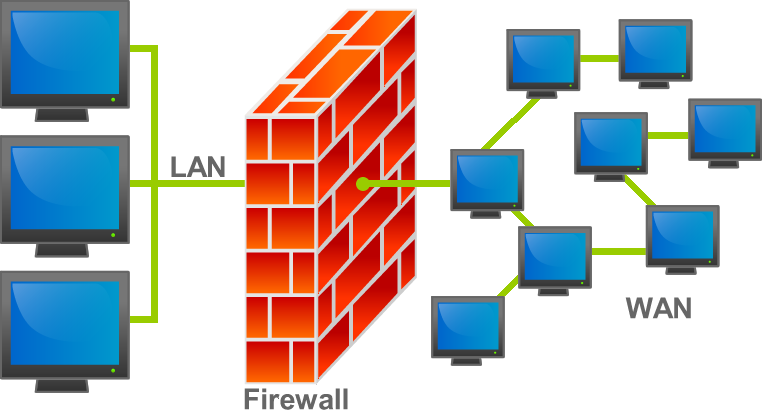
In any distributed computing system, time is the sole arbiter of truth, and cryptography is the sole guarantor of geography. Imagine attempting to diagnose a massive security breach where your database server claims an attacker exfiltrated data a full three minutes before your edge firewall recorded the initial intrusion. Without an absolute, universally synchronized metronome across all devices, digital forensics becomes mathematically impossible, cryptographic certificates expire prematurely, and authentication protocols immediately collapse. Similarly, as traditional network perimeters dissolve, we can no longer rely on the physical walls of a building to protect our data; we must construct invisible, encrypted bridges across the chaotic public internet to safely transmit information. Understanding how to engineer precise network time and implement secure virtual private network (VPN) access architectures is not merely an administrative chore—it is the foundational basis for establishing reality and trust in modern infrastructure.